Why Post-Quantum Security Matters Now
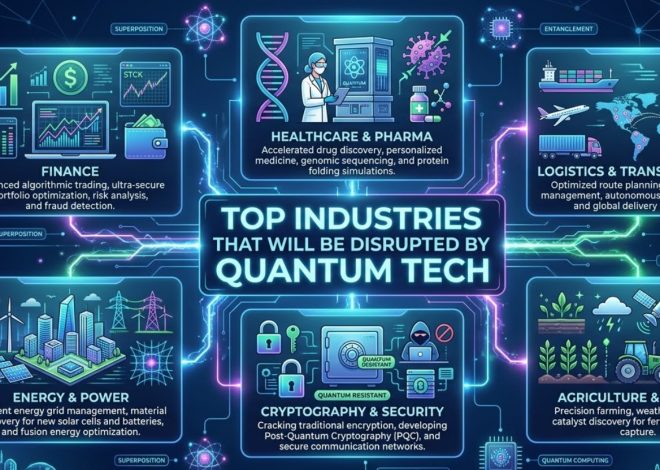
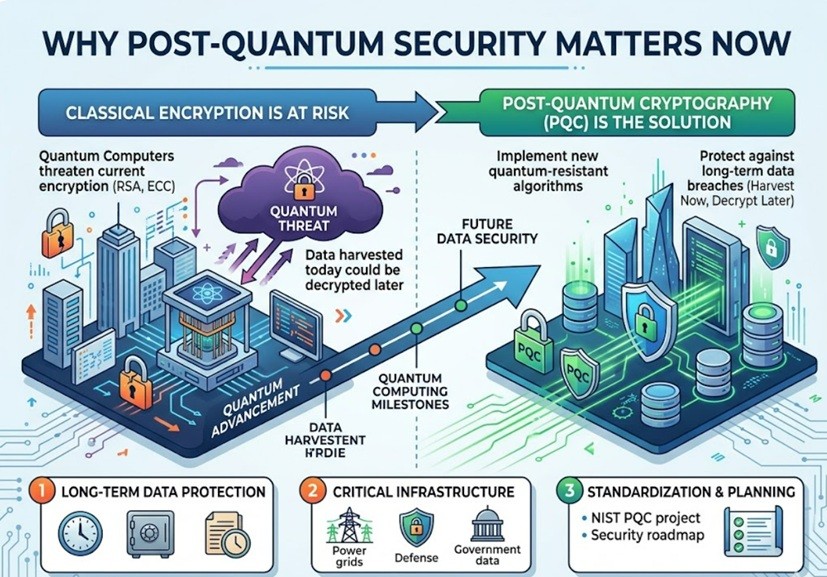
The race toward commonsense quantum computing is no longer science fiction. Governments, analysts, and major innovation companies are contributing billions into quantum innovations that may change pharmaceutical, back, coordinations, and manufactured insights. But nearby these breakthroughs comes a major cybersecurity concern: today’s encryption frameworks may in the long run ended up helpless to quantum attacks.
That is why post-quantum security has quickly gotten to be one of the most imperative themes in cybersecurity, cloud computing, and endeavor innovation. Businesses that get ready early will be superior situated to secure client information, keep up administrative compliance, and dodge future security disasters.
In this article, we will investigate what post-quantum security implies, why it things right presently, and how organizations can get ready for the another time of advanced security.
What Is Post-Quantum Security?
Post-quantum security, too called post-quantum cryptography (PQC), alludes to encryption strategies outlined to stay secure indeed against capable quantum computers.
Most advanced web security depends on cryptographic calculations such as RSA and ECC (Elliptic Bend Cryptography). These frameworks protect:
- Online banking
- Email communications
- Cryptocurrency wallets
- Cloud storage
- VPN connections
- E-commerce transactions
- Government databases
These conventional calculations are considered secure against classical computers since figuring huge numbers or understanding discrete logarithm issues takes an illogical sum of time.
However, quantum computers work differently.
Using standards like superposition and trap, quantum machines may inevitably unravel these scientific issues exponentially speedier than conventional computers.
This quantum calculation can effectively figure huge integrability and break numerous broadly utilized public-key cryptography systems.
That implies scrambled data considered secure nowadays may gotten to be lucid in the future.
Why Post-Quantum Security Things Right Now
Many individuals accept quantum dangers are decades absent. But cybersecurity specialists caution that organizations must start planning instantly for a few reasons.
1. “Harvest Presently, Unscramble Later” Attacks
One of the greatest concerns is the “harvest presently, unscramble later” strategy.
Attackers can collect scrambled information nowadays and store it until quantum computers gotten to be capable sufficient to decode it afterward. Delicate data such as:
- Medical records
- Financial transactions
- Government intelligence
- Intellectual property
- Legal documents
could stay important for a long time or indeed decades.
This makes an critical require for quantum-resistant encryption presently, not later.
2. Basic Framework Is at Risk
Modern foundation depends intensely on encryption frameworks helpless to quantum attacks.
Industries at tall hazard include:
- Banking and finance
- Healthcare
- Telecommunications
- Defense
- Energy grids
- Cloud computing
- E-commerce platforms
If quantum assaults compromise verification frameworks or scrambled communications, the results might incorporate gigantic monetary misfortunes, benefit disturbances, and national security threats.
3. Relocation Takes Years
Upgrading endeavor cryptography is not a speedy process.
Large organizations regularly utilize thousands of applications, gadgets, APIs, certificates, and communication frameworks. Supplanting powerless cryptographic frameworks can take numerous years.
Security specialists assess full movement to post-quantum cryptography may require:
- Extensive foundation audits
- Hardware upgrades
- Software rewrites
- Vendor coordination
- Compliance testing
- Long-term sending planning
Organizations that hold up until quantum computers arrive may as of now be as well late.
How Quantum Computers Undermine Current Encryption
Most web encryption depends on scientific issues that are troublesome for classical computers.
For illustration, RSA security depends on numbers factorization:
N=p×q
Where:
p and q are exceptionally expansive prime numbers
N gets to be troublesome to calculate classically
Quantum computers running Shor’s Calculation may figure these numbers significantly faster.
Similarly, elliptic bend cryptography depends on the hardness of discrete logarithm issues, which quantum frameworks may moreover illuminate efficiently.
This undermines conventions such as:
- HTTPS
- TLS
- SSH
- VPN encryption
- Digital signatures
- Blockchain authentication
In straightforward terms, much of today’s web believe framework may inevitably require replacement.
The Part of NIST in Post-Quantum Cryptography
The National Organized of Benchmarks and Innovation (NIST) has been driving worldwide endeavors to standardize post-quantum cryptographic algorithms.
After a long time of inquire about and testing, NIST chosen a few calculations for future cryptographic measures, including:
- CRYSTALS-Kyber
- CRYSTALS-Dilithium
- SPHINCS+
- FALCON
These calculations are outlined to stand up to assaults from both classical and quantum computers.
Major innovation companies are as of now joining these guidelines into their frameworks, including:
- Microsoft
- IBM
- Cloudflare
Their early selection signals that post-quantum relocation is getting to be an industry priority.
Industries That Require Post-Quantum Security Most
Financial Services
Banks and installment processors handle gigantic sums of touchy scrambled information daily.
Quantum assaults seem expose:
- Customer money related information
- Payment systems
- Trading infrastructure
- Fraud location systems
Financial teach are among the most punctual adopters of quantum-safe technologies.
Healthcare
Healthcare suppliers store long-term understanding records containing profoundly touchy information.
Medical information regularly remains profitable for decades, making it an perfect target for harvest-now-decrypt-later attacks.
Government and Defense
Government organizations oversee classified insights and national security communications.
Post-quantum encryption is progressively seen as a key national defense need worldwide.
Cloud Computing Providers
Cloud foundation companies secure gigantic volumes of venture data.
As businesses proceed moving workloads to the cloud, suppliers must guarantee long-term quantum-resistant protection.
Benefits of Early Post-Quantum Adoption
Organizations that start planning presently pick up a few advantages.
Improved Long-Term Security
Quantum-resistant calculations offer assistance secure delicate information distant into the future.
Regulatory Readiness
Governments are as of now examining future cybersecurity necessities related to post-quantum standards.
Early selection decreases compliance risks.
Customer Trust
Consumers progressively care almost advanced security and security.
Businesses that proactively embrace progressed security advances may pick up more grounded client confidence.
Reduced Relocation Costs
Gradual move arranging is frequently distant less costly than crisis framework substitutions later.
Challenges of Post-Quantum Migration
Despite its significance, transitioning to post-quantum security presents a few challenges.
Performance Overhead
Some quantum-resistant calculations require:
- Larger key sizes
- More bandwidth
- Increased computational power
This may affect framework performance.
Compatibility Issues
Older frameworks may not bolster unused cryptographic measures without major updates.
Rapidly Advancing Standards
Post-quantum cryptography is still advancing. Organizations must remain adaptable as benchmarks mature.
How Businesses Can Plan Today
Organizations do not require to freeze, but they ought to begin arranging immediately.
Key steps include:
1. Conduct a Cryptographic Inventory
Identify:
- Where encryption is used
- Which calculations are deployed
- Which frameworks contain long-term touchy data
2. Create Crypto Agility
Crypto dexterity implies planning frameworks that can swap cryptographic calculations rapidly when needed.
This adaptability will ended up fundamental amid post-quantum migration.
3. Take after NIST Standards
Monitor official direction and rising guidelines from NIST and worldwide cybersecurity agencies.
4. Work With Security Vendors
Many cybersecurity merchants are as of now testing quantum-safe technologies.
Businesses ought to assess seller roadmaps and future PQC support.
The Future of Cybersecurity Is Quantum-Resistant
Quantum computing has gigantic potential to reshape businesses and fathom complex logical issues. But it moreover speaks to one of the greatest cybersecurity disturbances in cutting edge history.
Post-quantum security is no longer a hypothetical dialog saved for analysts. It is quickly getting to be a commerce necessity.
Organizations that start planning nowadays will be distant superior prepared to secure delicate information, keep up client believe, and adjust to future administrative changes.
The move to quantum-resistant encryption may take a long time, but the time to begin is now.
As quantum computing proceeds progressing, post-quantum security will likely ended up one of the highest-value zones in cybersecurity, venture IT, and cloud foundation — making it a effective point for high-ECPM innovation substance and future-focused advanced distributing.